Create AWS IAM role using Terraform
This article explains how to create an IAM role in AWS using Terraform. To follow steps described in this article you need have below prerequisites configured.
- Terraform Installation
- AWS CLI Installation
- AWS Credentials Configuration
Create IAM role using Terraform
In this article we will perform following task to create an IAM role.
- Create Basic IAM role that can be assumed by Lambda Function
- Add inline policy to the created role
- Add managed policies to the created role
IAM role with assume role policy using Terraform
In the main.tf write below configuration and save main.tf.
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 3.27"
}
}
required_version = ">= 0.14.9"
}
provider "aws" {
profile = "default"
region = "us-east-1"
}
resource "aws_iam_role" "sample_role" {
name = "sample_role"
assume_role_policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = "sts:AssumeRole"
Effect = "Allow"
Sid = ""
Principal = {
Service = "lambda.amazonaws.com"
}
},
]
})
}
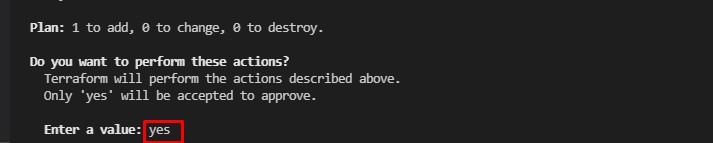
Run commands terraform fmt, terraform validate and finally terraform apply and type yes
in "Do you want to perform these actions" prompt.
terraform apply
Above command creates an IAM role named sample_role and attach assume role policy for AWS Lambda.
Add inline policy to the created role
Now the role has been created lets add one inline policy to the IAM role. Add below configuration in
resource block of main.tf
inline_policy {
name = "sample_inline_policy"
policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = ["ec2:Describe*"]
Effect = "Allow"
Resource = "*"
},
]
})
}
main.tf should look like as shown below.
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 3.27"
}
}
required_version = ">= 0.14.9"
}
provider "aws" {
profile = "default"
region = "us-east-1"
}
resource "aws_iam_role" "sample_role" {
name = "sample_role"
assume_role_policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = "sts:AssumeRole"
Effect = "Allow"
Sid = ""
Principal = {
Service = "lambda.amazonaws.com"
}
},
]
})
inline_policy {
name = "sample_inline_policy"
policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = ["ec2:Describe*"]
Effect = "Allow"
Resource = "*"
},
]
})
}
}
Run commands terraform fmt, terraform validate and finally terraform apply and type yes
in "Do you want to perform these actions" prompt.
terraform apply
After successful execution sample_role should have inline policy "sample_inline_policy" attached.
Add managed policies to the created role
Now we have role created and inline policy attached to it, in this step we will attach managed policy to the
role. Add below configuration to the resource block main.tf and save the file.
managed_policy_arns = ["arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess"]
main.tf should look like as shown below.
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 3.27"
}
}
required_version = ">= 0.14.9"
}
provider "aws" {
profile = "default"
region = "us-east-1"
}
resource "aws_iam_role" "sample_role" {
name = "sample_role"
assume_role_policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = "sts:AssumeRole"
Effect = "Allow"
Sid = ""
Principal = {
Service = "lambda.amazonaws.com"
}
},
]
})
inline_policy {
name = "sample_inline_policy"
policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Action = ["ec2:Describe*"]
Effect = "Allow"
Resource = "*"
},
]
})
}
managed_policy_arns = ["arn:aws:iam::aws:policy/AmazonS3ReadOnlyAccess"]
}
Run commands terraform fmt, terraform validate and finally terraform apply and type yes
in "Do you want to perform these actions" prompt.
terraform apply
After successful execution sample_role should have AmazonS3ReadOnlyAccess managed
policy
attached.
Category: AWS